In today’s threat landscape, businesses of all sizes face relentless attacks from phishing campaigns, CEO impersonation scams, ransomware, and other advanced threats that can cripple operations overnight. What once were isolated email scams have evolved into highly targeted intrusions — the FBI reported business email compromise losses exceeding $2.7 billion in recent years, and ransomware attacks occur every 11 seconds, costing companies millions in recovery and downtime. Without a comprehensive security stack and proactive monitoring, organizations are left vulnerable to breaches that not only disrupt business but expose them to regulatory fines, legal liability, and long-term reputational damage.
That’s why modern cybersecurity must be layered, automated, and continuously monitored. Our bundled managed services — including Endpoint Detection & Response (EDR), Patch Management, 24/7 SOC Monitoring, SaaS Security Alerts, Endpoint Backup, and Employee Phishing Training — work together to protect your people, systems, and data. From preventing threats before they strike to detecting unusual behavior in real time and rapidly responding to incidents, we give your business the tools and expertise it needs to stay secure, compliant, and resilient in an era where threats never rest.
Our comprehensive security and monitoring stack ensure out clients are protected and meeting modern compliance requirements.
Device Protection

Security & Risk Mitigation
Unpatched software is a leading cause of data breaches. Approximately 60% of breaches involve vulnerabilities where a patch was available but not yet deployed. Patching closes these "security holes" to prevent ransomware, malware, and unauthorized access. Many industry standards (e.g., HIPAA for healthcare, PCI DSS for payments, and GDPR for data privacy) mandate timely patching. Failure to comply can lead to heavy fines, legal penalties, and loss of security certifications.
WavTeK’s RMM Agent scans devices for patches and based on priority and severity of impact allows automated installation or scheduled application. Keeping your systems protected and compliant.
Next-Generation Antivirus Engine
Beyond signature-based security, incorporating AI and machine learning for dynamic threat response.
Proactive security against domain-based cyberthreats and enforcement of web access policies.
Automatic, real-time identification, quarantine and cleansing of malware-infected systems.
Optimal security without compromising system performance, using minimal system resources.
Real-Time Response.

WavTeK’s EDR
Endpoint Detection and Response (EDR) systems act like a 24/7 security squad for your devices (laptops, phones, servers). While traditional antivirus acts as a "bouncer" checking for known bad actors, EDR is a high-tech surveillance system that watches for suspicious behavior in real-time.
Instead of just looking for known "signatures" (stolen "IDs"), EDR uses machine learning to identify anomalies.
It learns what "normal" looks like for your device and flags deviations, such as a sudden mass encryption of files (ransomware).
It can stop never-before-seen threats based solely on their suspicious actions.
When a threat is detected, EDR doesn't just send an alert; it can take action instantly to minimize damage.
It can automatically "quarantine" your device from the rest of the network, preventing a virus from spreading to your coworkers' computers. It can kill malicious processes or delete harmful files as soon as they are identified.
Cloud Protection

WavTeK SaaS
According to a report by IBM, it takes an average of 204 days to detect a cyber security breach. Oftentimes users have no idea there’s someone lurking in the background, watching their every move. It’s not until something happens, such as payments being redirected or files going missing, that someone raises an alarm.
SaaS Alerts identifies activity that a typical hacker would take, like setting up an email forwarding rule or changing admin credentials, and alerts you immediately.
The faster you can notice a cyber security issue, the faster you can rectify it. And those minutes can mean the difference between a breach that leads nowhere — or one that leads to major data theft that requires hours of documentation and endless cleanup.
With SaaS Alerts, security breaches can now be detected much more quickly, so your team can act fast.
SaaS Alerts automatically responds to detected threats and account compromises, temporarily disabling the account and blocking new login attempts. Automated incident response occurs within minutes of detection and provides detailed forensic logs of compromised data and remediation steps.
Account Protection
E-Mail and Fraud Defense
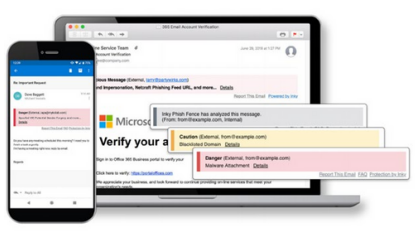
Phishing is still the number one cause of data breaches for companies, and the hooks are getting sharper. INKY’s innovative technology excels where legacy solutions fall short.
Our Inky mail protection:
· Parses every HTML email and reconstructs it to ensure malicious content doesn’t make it through.
· Sees emails much like a person would — but better — so even very convincing forgeries get blocked.
· Builds dynamic profiles and behavior models of senders to block impersonation attempts.
· Builds dynamic profiles and behavior models of senders to block impersonation attempts.
· Blocks malware and viruses at the server level
Like a security coach, the INKY Email Assistant signals suspicious behaviors with interactive banners that guide users to take safe action. The assistant turns real emails into teachable moments, training users on potential threats and empowering them to report emails on any device or email client.
Dark-web mONITORING
Dark Web Monitoring
Are your company’s user credentials on the dark web?
Thousands of email addresses, passwords and other sensitive data land on the dark web every day, creating risk for your business — and you may not even know about a vulnerability until it’s too late.
WavTeK’s DarkWeb Scanning ensures the greatest amount of protection with 24/7/365 human and machine-powered monitoring of business and personal credentials, including domains, IP addresses and email addresses.
We uncover your compromised credentials in dark web markets, data dumps and other sources, and alert you to trouble fast, giving you the advantage to act before cybercriminals do.
end point bACKUP
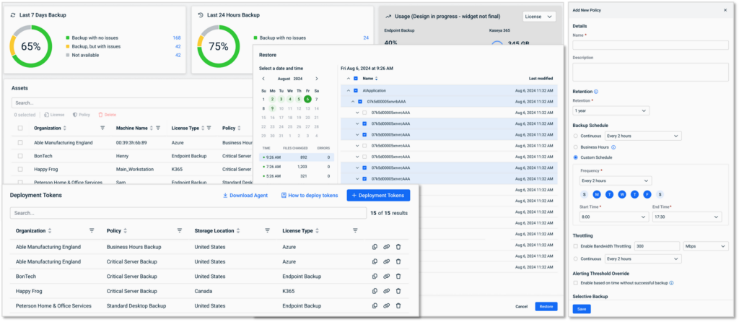
WavTeK Cloud backup
Endpoint Detection and Response (EDR) systems act like a 24/7 security squad for your devices (laptops, phones, servers). While traditional antivirus acts as a "bouncer" checking for known bad actors, EDR is a high-tech surveillance system that watches for suspicious behavior in real-time.
Instead of just looking for known "signatures" (stolen "IDs"), EDR uses machine learning to identify anomalies.
It learns what "normal" looks like for your device and flags deviations, such as a sudden mass encryption of files (ransomware).
It can stop never-before-seen threats based solely on their suspicious actions.
When a threat is detected, EDR doesn't just send an alert; it can take action instantly to minimize damage.
It can automatically "quarantine" your device from the rest of the network, preventing a virus from spreading to your coworkers' computers. It can kill malicious processes or delete harmful files as soon as they are identified.
24/7 Security Monitoring

WavTeK’s Managed SOC
Fortify your network from unauthorized access and breaches that bypass lesser security measures. Our real-time monitoring system keeps a watchful eye out for suspicious activity, enabling timely responses.
Managed SOC services operate by continuously monitoring an organization's IT environment to identify and respond to potential security threats. We use advanced tools and technologies to analyze data, detect anomalies, and generate alerts. Expert SOC analysts then investigate these alerts, determine the severity of the threats, and take appropriate action to mitigate them on the customer's behalf.
Minimize business disruptions and alleviate risks with swift, organized responses to cyber incidents. WavTeK’s security experts monitor around the clock to assess threats, review data, and promptly act upon breaches.
Includes:
Continuous threat monitoring
Human analyst investigation
Rapid response to alerts
uSER tRAINING
User Security Training
An estimated 90% of security breaches are caused by human error, yet many organizations don’t have a program in place to protect the human attack surface. With WavTeK’s security awareness training and phishing simulation solution, you can reduce your organization’s chance of experiencing a cybersecurity disaster by up to 70%.
· Educate and empower employees to spot and stop phishing threats and follow cybersecurity best practices.
· Automate training campaigns and reporting for effortless, set-it-and-forget-it training that gets results.
· Satisfy requirements for cyber liability insurance purchase or renewal by having strong cybercrime protections — like a user security awareness training program — in place.
· Maintain compliance with industry regulations and avoid high fees for non-compliance by conducting ongoing security awareness training.
