Identify Vulnerabilities Before Attackers Do
What We Do:
We simulate real-world attack scenarios to evaluate your environment from an attacker’s perspective.
External vulnerability scanning
Internal network assessment
Credential exposure testing
Phishing susceptibility testing
Firewall and perimeter review
Active Directory and privilege analysis
Endpoint security validation
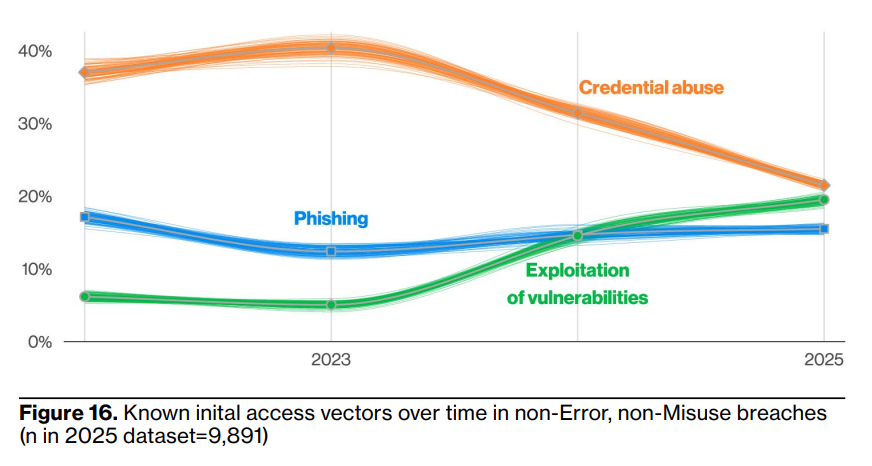
Upatched vulnerabilities and zero-days are the number one initial access tactique that ransomware groups use. Using compromised credentials comes second, according to Statista:
33% exploited a vulnerability to gain access
23% used compromised credentials
19% of ransomware incidents had a malicious email as root cause
18% started with phishing
7% used brute force
Cyber threats don’t break in — they log in.
Most breaches occur because of misconfigurations, weak credentials, or overlooked vulnerabilities that go undetected until it’s too late.
Our Security Assessment and Penetration Testing services are designed to proactively uncover those weaknesses before they can be exploited.
❋ Real-World Testing, Not Just ReportsWe don’t just run automated scans and hand you a generic report.
❋ We:Validate findings manually
Prioritize risks based on real impact
Validate findings manually
Provide clear remediation steps
Review results with your team
❋ Why It MattersWithout testing, you’re operating on assumptions.
Identify gaps before ransomware does
Validate your current security investments
Meet compliance and insurance requirements
Reduce attack surface and business risk
❋ Built for Businesses That Take Security SeriouslyWhether you're preparing for cyber insurance, compliance audits, or just want to know where you stand — we give you clarity and a path forward.
Contact us today to get started.
In early 2026, ransomware remains a dominant global threat, with costs projected to reach $74 billion annually. This represents a 30% increase from 2025, driven by evolving AI-enabled tactics and a shift from simple encryption to complex multi-stage extortion campaigns.
Don’t let your company find out about its vulnerabilities only after it’s too late.
